Setup Sftp server on Centos 7
SFTP (SSH File Transfer Protocol) is different from the FTP type although it supports all the FTP clients. SFTP has been implemented to add a security layer, it presents an access level vulnerability since, being a standard, it grants total access to system users for file transfer and use of the Shell.
On certain occasions, a Systems Administrator may need to create a user account and restrict their access to only manage their own files via sFTP, but not be able to login to the system using any other means.
We just require the prebuild SSHd package that got already installed during installation on the server.just for conformation check below packages are installed or not.
[root@lampblogs ~]# rpm -qa|grep ssh
openssh-7.4p1-16.el7.x86_64
openssh-server-7.4p1-16.el7.x86_64
openssh-clients-7.4p1-16.el7.x86_64
libssh2-1.4.3-10.el7_2.1.x86_64Step 1: create user
[root@lampblogs ~]# useradd -s /sbin/nologin sftpuser
[root@lampblogs ~]# passwd sftpuserStep 2: create directory and setup permissions
[root@lampblogs ~]# mkdir -p /var/sftp/uploadChange the ownership of the files directory to sftp user. So that sftpuser can read and write on this directory.
[root@lampblogs ~]# chown sftpuser:sftpuser /var/sftp/uploadAnd set the owner and group owner of the /var/sftp to root. The root user has read/write access on this access. Group member and other account have only read and execute permissions.
[root@lampblogs ~]# chown root:root /var/sftp
[root@lampblogs ~]# chmod 755 /var/sftp
Step 3: configure ssh for sftp
Edit ssh config file as below
[root@lampblogs ~]# vi /etc/ssh/sshd_configFind the line
Subsystem sftp /usr/libexec/openssh/sftp-serverReplace it with below
Subsystem sftp internal-sftpAdd following lines at the end of the file
Match User sftpuser
ForceCommand internal-sftp
PasswordAuthentication yes
ChrootDirectory /var/sftp
AllowTcpForwarding no
X11Forwarding no
Save the configuration and restart SSH service to apply changes.
Then restart ssh service
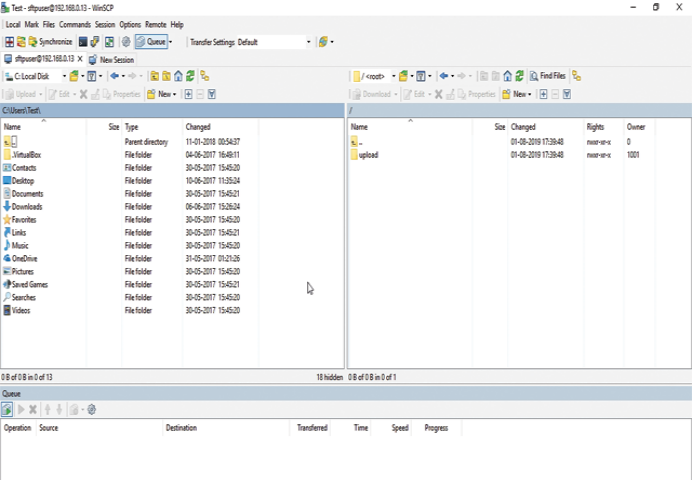
[root@lampblogs ~]# systemctl restart sshdStep 4: Test Sftp connection using winscp or filezilla